Identity becomes the control plane for enterprise AI security
Become a member of the event that is trusted by business leaders for almost two decades. VB Transform brings together the people who build the real Enterprise AI strategy. Leather
Stolen references are responsible for 80% of the breaches of the company. Each major security seller is merged with the same conclusion: Identity is now the control surface for AI security. Scale only requires this shift. Enterprises that manage 100,000 employees will handle more than a million identities when AI agents enter the production.
Traditional Identity Access Management (IAM) Architectures cannot scales to secure the proliferation of agentic AI. They were built for thousands of human users, not millions of autonomous agents who work quickly with permissions at human level. The response of the industry represents the most important security transformation since the application of Cloud Computing.
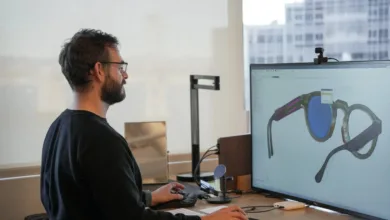
Provision -based authentication replaces Hardwaretokens
Use leading sellers now Bluetooth low energy (BLE) between devices and laptops to prove physical proximity. Combined with cryptographic identities and biometrics, this four-factor creates authentication without the need for hardwaretokens.
Cisco’s duo demonstrates this innovation to scale. Their proximity verification supplies phishing-resistant authentication with the help of BLE-based proximity in combination with biometric verification. This possibility, unveiled Cisco Live 2025represents a fundamental shift in authentication architecture.
Microsoft’s Entra ID Handles 10,000 AI agents in a few pilot programs and processes 8 billion authentications every day. “Traditional directory services were not archived for autonomous systems that work at this speed,” says Alex Simons, CVP of Identity at Microsoft.
Ping Identities Davinci -orchestration platform pushes further. The system processes more than 1 billion authentication events every day, where AI agents are good 60% of the traffic. Each verification is completed in fewer than 200 milliseconds while retaining cryptographic evidence.
Catching behavioral analyzes in real -time compromised agents
Crowdstrike Treats AI agents like any other identity threat. Their Falcon platform determines behavioral bases for each agent within 24 hours. Activate deviations within a few seconds of automated inclusion.
“When an AI agent suddenly has access to systems outside the established pattern, we treat it identically on a compromised employee reference,” Adam Meyers, head of opponents at Crowdstrike, told Venturebeat. The platform follows 15 billion AI-related events in customer environments every day.
That speed is important. Crowdstrike 2025 Global threat report Documents that opponents reach initial access in less than 10 minutes. They move laterally over 15 systems within the first hour. AI agents who work with compromised identities reinforce this damage exponentially.
Identity file prevents catastrophic failures
Companies on average 89 different identity stores in cloud and on-premises systems, according to Gartner. This fragmentation creates blind spots that opponents operate daily. The solution applies network principles to identity infrastructure.
Oktas Advanced Servert access implements redundancy, load balancing and automated failover with identity providers. When primary authentication failed, activate secondary systems within 50 milliseconds. This is mandatory when AI agents perform thousands of operations per second.
“Identity is security,” said Todd McKinnon, CEO of OKTA, on Octane 2024. “When you move AI to production, you give agents access to real systems, real data and your customer data. One affected agent identity cascades about millions of automated actions.”
Zero trust scales for agent’s proliferation
Palo Alto Networks’ Cortex Xsiam completely leaves the perimeter defense. The platform works in the assumption of continuous compromise. Each AI agent undergoes verification before any action, not just with the first authentication.
Mike Riemer, Field Ciso on IvantiStrengthened the zero confidence approach in a recent interview with Venturbeat: “It works according to the principle of ‘Never Trust, always check’. By adopting a zero trust architecture, organizations can ensure that only verified users and devices have access to sensitive data and applications.”
Cisco’s Universal ZTNA Expands this model to AI agents. The platform is expanding zero confidence outside man and IoT devices to include autonomous AI systems, offering automated discovery and delegated authorization to scale.
Automated Playbooks immediately respond to identity abnormalities. When malware causes irregularities authentication, Xsiam attracts access and launches forensic analysis without human intervention. This zero-late sponge becomes the operational basic line.
Zscaler CEO Jay Chaudhry identified the core vulnerability Zenith Live 2025: “Network protocols are designed to allow trusted devices to communicate freely. AI arms these legacy architecture on a scale. Opponents make phishing campaigns that compromise the identities of the agent faster than people can respond.”
Universal ZTNA frameworks make the implementations of million agent possible
The architectural requirements are clear. Universal Zero Trust Network Access (ZTNA) Frameworks in the industry offer four options that are essential for AI environments.
The implementation of Cisco shows the required scale. Their universal ZTNA platform performs automated discovery scans every 60 seconds and catalogs new AI implementations and authorization sets. This eliminates blind spots on which attackers focus. The delegated authorization engine of Cisco maintains the least-privilege limits by policy engines that process 100,000 decisions per second.
Extensive audit paths record every agent action for forensic research. Security teams use platforms such as Cisco’s can reconstruct incidents about millions of interactions. Native support for standards such as the Model context protocol Ensures interoperability as the ecosystem evolves.
Ivanti’s approach complements these possibilities with AI-driven analyzes. Daren Goeson, SVP of product management at Ivanti, emphasizes: “AI-driven end point security aids can analyze enormous amounts of data to detect anomalies and predict potential threats faster and more accurately than any human analyst. These tools offer a clear visibility of devices, users and networks, users and networks.”
Cisco’s AI security architecture sets the industrial direction
The AI Secure Factory from Cisco positions them as the first non-Nvidia silicon provider in Nvidia’s reference architecture. By combining post-quantum coding with new devices, Cisco builds up infrastructure to protect against threats that do not yet exist. The Enterprise Takeaway: Security is not optional; It is architectural.
At Cisco Live 2025, the company unveiled an extensive identity and AI security strategy that tackles each layer of the stack:
| Announcement | Core problem solved / strategic value | Technical details | Availability |
| Hybrid mesh firewall (incl. Hypershield) | Distributed, substance-native security; Moves security from the circumference to the network fabric | EBPF-based enforcement; Hardware – | New firewalls: October 2025 |
| Live protect | Close the “45-day patch versus 3-day exploit” gap with rapid vulnerability at kernel-level shielding | Real-time patching without reboots | Nexus OS: September 2025 |
| Splunk: free firewall log intake | Reduces the SIEM costs to 80%; stimulates the adoption of Cisco Firewall | Unlimited Log -Innea in Cisco Firewalls | Aug 2025 August |
| Splunk: Positability for AI | Offers critical visibility in AI pile performance | Monitors GPU use and model performance | Sept 2025 |
| Duo IAM | Evolves from MFA to a complete security-first IAM platform | User directory, SSO, identity routering engine | Now available |
| DUO: Nearbyity verification | Supplies phishing-resistant authentication without hardware chefs | Ble-based proximity, biometric verification | Part of the new Duo IAM |
| DUO: Identity Resilience | Focus on critical IDP risks | Redundancy, load balancing and automated failover | In development |
| Cisco Universal ZTNA | Expands zero confidence to people, IoT/OT devices and AI agents | Automated discovery, delegated authorization | Constant evolution |
| Open-sourced security AI model | Democratizes AI defense; 8b parameters correspond to 70b model performance | Runs on CPU; 5B Security Tokens Training | Available (hugging face) |
| AI Defense and Nvidia Partnership | Protects AI -Development pipeline | NVIDIA NIM MicroServices Optimization | Now available |
| Security after the quantum | Future -proof against quantum attacks | Macsec and IPSEC coding | New devices (June 2025) |
| Identity intelligence | Continuous behavioral monitoring | AI-driven anomalia detection | Part of Security Cloud |
| Security of access | Converge VPN and ZTNA possibilities | Wolk-delivered secure access service Edge | Now available |
Cross-liver-collaboration accelerates
The Cloud Security Alliance Zero Trust Advancement Center Now includes every major security seller. This unprecedented cooperation makes uniform security policy on various platforms possible.
“Security suppliers must agree against common threats,” emphasized George Kurtz, CEO of Crowdstrike, during a recent platform strategy discussion. “The data -oriented approach wins, given how fast opponents and threats are evolving.”
Cisco President and CPO Jeetu Patel repeated this sentiment in an interview with Venturebeat: “Security is a condition for the approval of AI. If people do not trust the system, they will not use it.”
The organizational challenge remains. Robert Grazioli, CIO at Ivanti, identifies the critical barrier: “CISO and CIO coordination will be crucial in 2025. This cooperation is essential if we have to protect modern companies effectively. Executives must consolidate resources – budgets, personnel, data and technology – to improve the security attitude of an organization.”
The identity account
When Cisco, Okta, Zscaler, Palo Alto Networks and Crowdstrike draw independently to identical conclusions about identity architecture, the confirmation is no coincidence.
Identity infrastructure determines security results. Organizations are confronted with two options: architectural identity such as the control surface or accept breaches as inevitable. The gap between AI implementation speed and the maturity of identity protection narrower daily.
Three promotions can’t wait. Audit the identity and permissions of each AI agent within 30 days. Implement continuous verification for all non-human identities immediately. Set up 24/7 identity security activities to prevent opponents from exploiting gaps.
The seller’s consensus sends a clear and unmistakable signal. Identity has become the control surface for AI security. Companies that do not adapt will spend 2025 managing infringements instead of innovation.
Source link